Zedly Shield: The Safety Layer for OpenClaw.
Shield runs on your machine and automatically blocks PII leaks, risky commands, and prompt injection — before your OpenClaw agent can do any damage. No code to write, no YAML to edit.
Built for anyone running OpenClaw — from solo operators worried about data leaks to enterprise security teams that need audit evidence.
Stops PII leaks
Emails, SSNs, credit cards, and API keys never reach the model.
Blocks risky commands
Agents can't run dangerous shell commands or write to the wrong files.
Audit trail for compliance
Every action logged with a tamper-evident chain. Export for auditors.
Runs on your machine
Nothing sensitive goes to Zedly or the cloud. Policy stays local.
How Shield Enforces the Agent Lifecycle
Every action your OpenClaw agent takes passes through Shield first.
Agent Requests Tool Call
LLM decides to run exec, read, write, or HTTP
Shield Intercepts
Every shell, file, and HTTP call lands here first
Policy Engine Evaluates
Block / allow / redact based on rules
Command Executes (or Blocked)
Dangerous calls stopped, PII stripped from results
Log + Forward Event
Tamper-evident log, plus forwarded to your dashboard
What Shield Does
Nine layers of runtime protection for agentic workflows.
PII Redaction
Emails, SSNs, and credit card numbers are detected and tokenized before they reach the model provider. Rehydration happens locally after the response returns.
Read the guide →Policy-Based Blocking
Block dangerous shell commands, restrict file write paths, and deny network access from unattended cron sessions. Rules match tool name and argument patterns.
Read the guide →Human Approval Gates
Queue sensitive operations for human review before execution. Policy decides which tool calls need approval based on tool type, arguments, and session context.
Read the guide →Immutable Audit Log
Every event is a JSON line with a SHA-256 hash linking it to the previous event. Tamper with one line and the chain breaks. Generate technical evidence that supports your internal compliance and audit processes.
Read the guide →Fleet Dashboard
Manage multiple Shield instances from a single control plane. See events, blocks, and redactions across all deployments. Push policy changes from the cloud.
Read the guide →Ops Visibility
Session runs with status, duration, and tool counts. Event timeline filterable by type. Cost tracking per job, tool, and model.
Read the guide →API Key & Secret Detection
12 provider-specific patterns detect OpenAI, Anthropic, Google, AWS, GitHub, Stripe, and other API keys before they reach the model. Always on by default, zero configuration required.
Read the guide →Content Deny Lists
Block or redact organization-specific keywords, project names, and regex patterns. Define what cannot leave your environment, whether that is a project codename or an internal document ID format.
Read the guide →Mandatory Execution Boundary
Shield sits between your agent and the outside world. OpenClaw routes every shell, file, and HTTP call through Shield first, so there's no way for a misbehaving agent to skip the safety checks.
Read the guide →Security Principles
How Shield earns trust in sensitive environments.
Policies run on your machine. Sensitive content never transits through Zedly.
SHA-256 hash chain on every event. Modification breaks the chain.
Block by default. Approve by exception. Scope by tool, path, and session.
Sensitive operations queue for review before execution.
Only metadata forwarded to the cloud. Raw content stays on your machine.
Who is Shield for?
One daemon, three different reasons to run it.
Business owners & operators
Peace of mind that your OpenClaw agent won't accidentally email a customer's SSN to OpenAI, wipe a folder, or act on a malicious email. Turn it on, forget about it.
Compliance & risk teams
Exportable, tamper-evident audit trail. PII redaction on by default. Policy-as-code so your rules are version-controlled. Evidence you can hand an auditor.
Engineers & IT leads
Single compiled Rust binary. No Node.js, no plugin graph. A UDS socket boundary OpenClaw cannot bypass. Runs as systemd or launchd service.
More Than Redaction: Evidence-First Governance
OpenClaw has plugins for PII and command blocking. Shield adds what they don't: tamper-evident audit, prompt injection detection, and fleet visibility.
SHA-256 hash chain on every event. Exportable evidence for your internal compliance and audit processes. OpenClaw core declined a similar proposal; Shield ships it.
30+ pattern-based scans on messages and tool results. Flag and warn before the model sees injected instructions. OpenClaw has an open request for this; Shield has it today.
One dashboard for all Shield instances. Event timelines, blocks, and redactions across every deployment. No other OpenClaw plugin offers cross-instance visibility.
PII, shell blocking, prompt injection, approval gates, and audit in one compiled daemon. No Node.js, no plugin dependencies — just one binary.
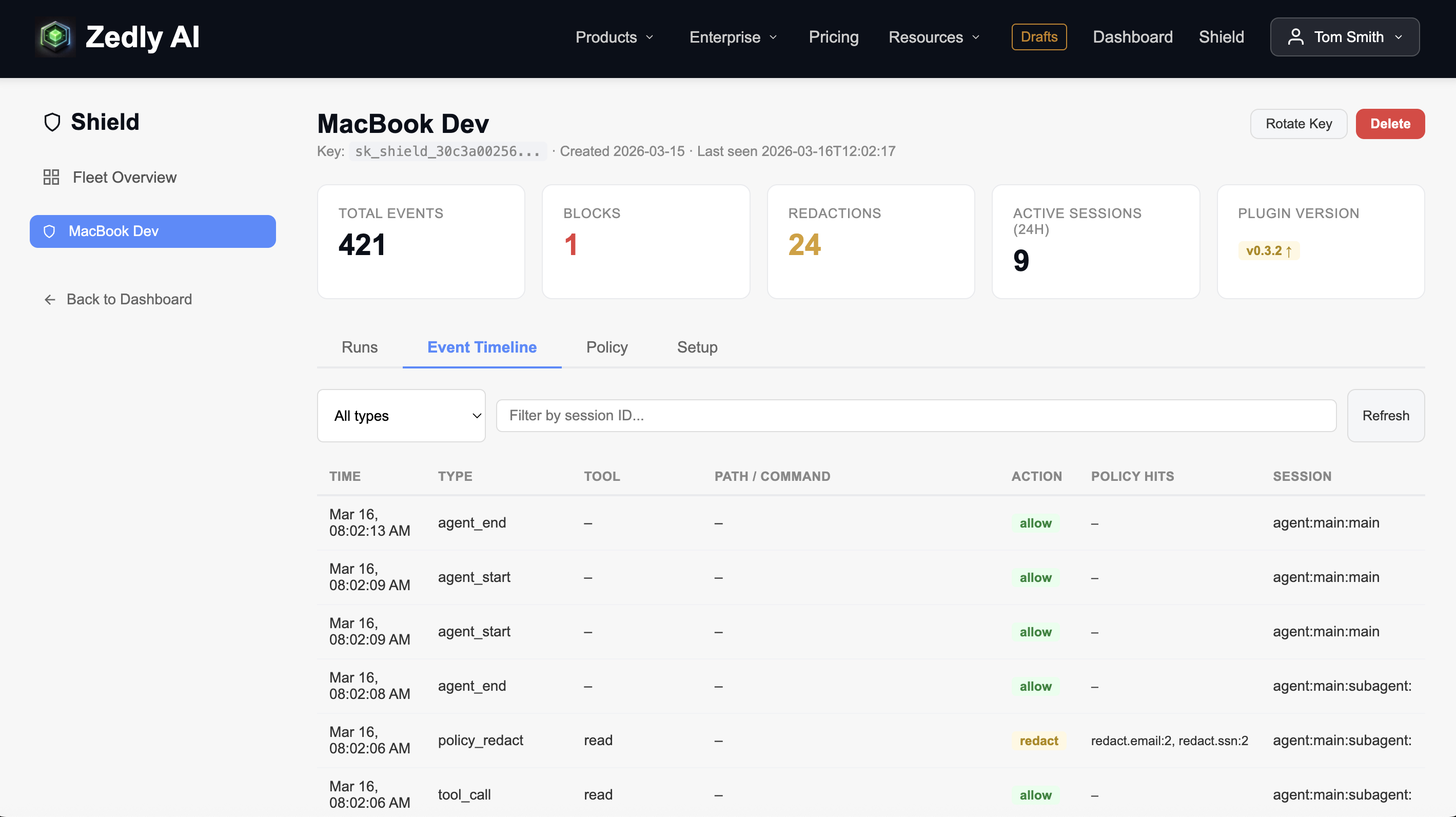
Cloud Dashboard for Your Fleet
One place to see what every Shield instance is doing. View session runs, event timelines, policy blocks, and PII redactions across all deployments. The daemon forwards event metadata to the dashboard automatically.
- Fleet-wide stats: instances, events, blocks, redactions
- Session run table with status, duration, and tool breakdown
- Event timeline filterable by type and session
- Policy editor with save and sync to instances
- API key management and instance provisioning
How It Compares
What you get with Shield vs. the alternatives.
| Capability | No Protection | DIY Middleware | Zedly Shield |
|---|---|---|---|
| PII redaction (email, SSN, credit card) | None | Build your own regex | Built-in, on by default |
| Tool-call blocking | None | Custom hook code | Policy-as-JSON rules |
| Human approval gates | None | Build approval queue | Policy-based interception via daemon |
| Audit trail integrity | Terminal scrollback | Append-only log file | SHA-256 hash chain |
| Multi-instance dashboard | N/A | Build from scratch | Fleet view, per-instance drill-down |
| Install & upgrade | N/A | Manual deployment | curl + systemctl / launchctl |
| Policy-as-code | None | Hardcoded logic | JSON config, cloud-synced |
| API key / secret detection | None | Build your own regex | 12 providers, on by default |
| Content deny lists | None | Hardcoded keyword lists | Configurable keywords + regex |
| Mandatory execution boundary | None | N/A | Rust daemon, cannot be bypassed |
Get Started
The fastest path: create a free account and let Zedly Setup install Shield for you. Prefer to install the daemon yourself? Expand below.
Developer install — curl + systemd / launchd (click to expand)
1 Create your Shield instance
Create a free account, open the Shield dashboard, and create a new instance. Copy the API key it generates.
2 Download the daemon
Single binary, no Node.js or npm required. Also available from GitHub Releases.
3 Configure
Write this to ~/.openclaw/shieldd.toml. All protections (PII redaction, shell blocking, audit logging) are on by default. The [forward] section is optional — it sends event metadata to the cloud dashboard.
4 Start as a service
Verify with shieldd status or curl http://127.0.0.1:4017/health. Events will appear in your dashboard immediately.
↑ Upgrade later
New protections are enabled by default on upgrade. No config edits needed.
Shield Guides
Deep dives on each layer of agentic AI security.
How to Add PII Redaction to OpenClaw
Detect, tokenize, and rehydrate emails, SSNs, and credit card numbers before data leaves your environment.
OpenClaw Tool Call Audit Log
Capture every agent action with structured event logging: tool name, arguments, result, and timing.
OpenClaw Immutable Audit Log
Build a tamper-evident event chain with SHA-256 hashing. Detect tampering, export for compliance.
Human Approval for Sensitive Actions
Add gates before tools execute. Policy-based blocking, argument-pattern matching, and structured audit events.
OpenClaw Cron Run History Dashboard
Track every scheduled job: start time, duration, exit status, tool calls, and policy blocks.
OpenClaw Tool Call History Dashboard
See what your agents actually do. Filterable timeline of every tool invocation across sessions.
OpenClaw Cost Dashboard
Track agent spend by job, tool, and model. Spot runaway costs before they hit your invoice.
OpenClaw DLP Data Loss Prevention
On-device data loss prevention for agentic AI. Three architectural approaches compared, with deployment guide.
Frequently Asked Questions
shieldd) that provides local-first enforcement for agentic AI workflows. It runs alongside agent runtimes like OpenClaw to redact PII, block dangerous tool calls via policy, and produce tamper-evident audit logs. All policy enforcement and redaction happens on your machine — sensitive content never passes through Zedly infrastructure.shieldd) alongside the OpenClaw Gateway. OpenClaw routes commands to the daemon via a Unix domain socket. The policy engine evaluates every tool call — blocking dangerous commands, redacting PII, and logging tamper-evident events — before the command executes. Configure with shieldd.toml and run as a system service.shieldd binary for your platform from zedly.ai/dl/shield/ or GitHub Releases, replace the existing binary at ~/.openclaw/bin/shieldd, and restart the service. New protections are enabled by default — no config edits needed.Start Using Zedly Shield
Create a free account to access the dashboard, manage instances, and see events from your Shield daemon.
Interested in fleet management, enterprise features, or policy packs?
You're on the list.
We'll reach out when enterprise access opens. In the meantime, install the daemon and start protecting your OpenClaw deployment locally.
No spam. We'll email you when enterprise features launch.
Protect Your Agentic AI Workflows Today
Install the daemon for free. Create your account to see events in the dashboard.